AT&T Data Breach Highlights Critical Need for Enhanced Business Cybersecurity
The recent security breach at AT&T, where hackers reportedly accessed extensive call and text records from almost all its wireless customers, including numerous business accounts, has sent shockwaves through the corporate world. This significant security incident accentuates the necessity for stringent cybersecurity protocols across industries. It is essential for business leaders to grasp the implications […]
Log4j Vulnerability is Almost Guaranteed to Impact Your Business

The major Log4j vulnerability has a widespread impact across various technology. We can’t stress how serious this is, and your business needs to take action right away. What is Log4j? We’ll keep it simple; programmers can utilize different programming languages when creating software. One of these languages is called Java, and in Java, programmers have […]
The Major Takeaways from the Big Facebook Outage of 2021

Unless you live under a rock and somehow missed it, Facebook experienced an outage, an inconvenience that kept users from accessing its services all over the world. Perhaps to your surprise, the real ramifications of this outage have nothing to do with people not being able to share pictures of their cats or yell at […]
How the Semiconductor Shortage is Influencing Supply Chains
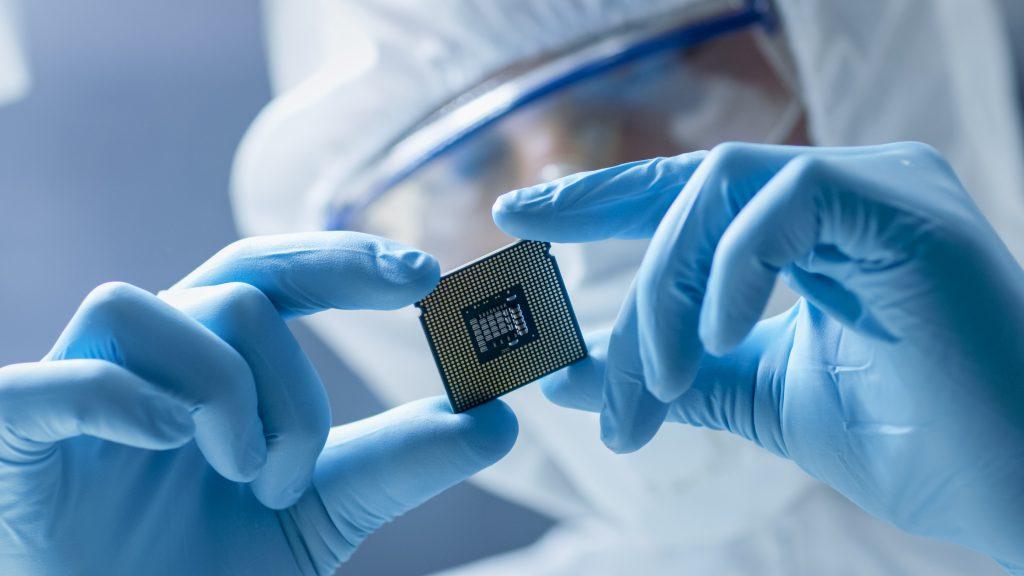
You may have noticed the recent price increase for consumer and business electronics, and it’s all caused by issues related to the global semiconductor shortage. How have these supply chains, stable for so long, been dealt such a severe blow to the point where acquiring new computers and networking equipment is so challenging? Read on […]
BlackRock Trojan: Aggressive Viral Menace For Android Device Users

A new attack on android applications known as the BlackRock trojan has already targeted over 300 applications on the android operating system, including banking, social media, and dating applications. Any application with payment features, which is most nowadays, has been targeted and users credit card information has been compromised. How does this all work though, […]

