Tip of the Week: Scan Picture or Document to PDF in Android

Many people don’t realize that their mobile device can double up and offer them many of the same great features that a PC or laptop could. A hidden secret that very few people take advantage of is the fact that Google Drive offers you the chance to scan a document or picture and create a […]
Tip of the Week: How to Remove or Hide Desktop Icons
For many people, the desktops of computers or laptops often get extremely cluttered with various icons and files. Fortunately, there is a way to delete and/or hide those icons from your screen view which will allow for increased productivity and improved organization. Continue reading to learn how this can be done using a Windows PC. […]
How to Record Screenshots, Audio, and Video on Windows 10
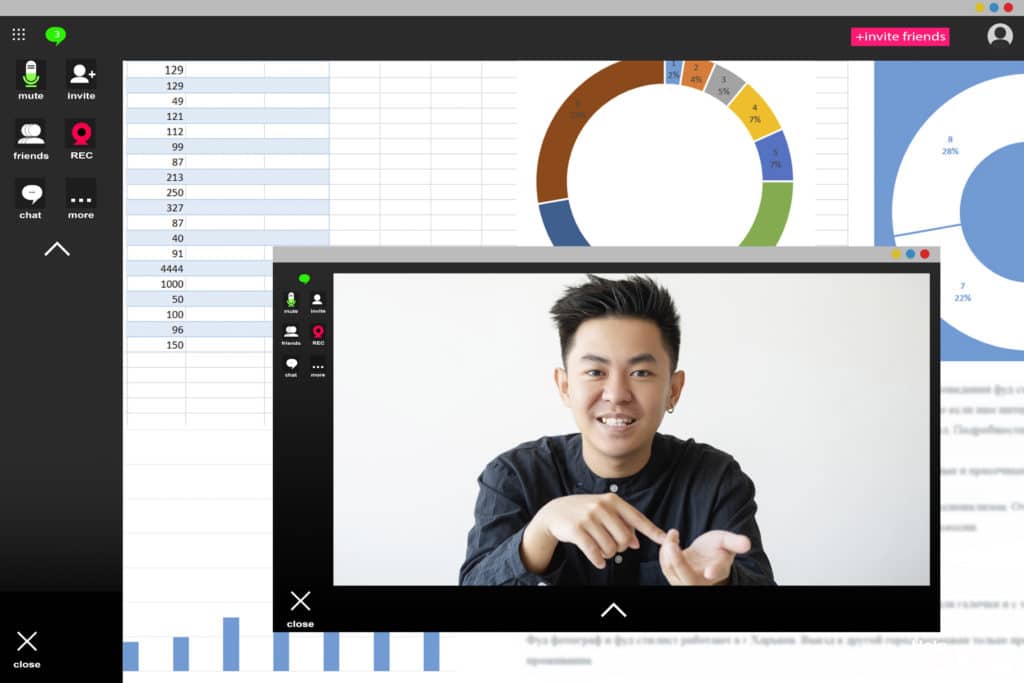
If you have ever had to write up a report or process for a particular task, you know that images can go a long way toward helping people understand what exactly needs to be done. For Windows 10 users, there is a built-in tool that you can utilize to take screenshots, record video, and even […]
6 Cyber Security Tips for Remote Workers

As we transition into the #WorkFromHome life, staying safe remains our top priority. Don’t forget to consider data security and cyber threats while working remote. Viruses of a different kind can throw a wrench in productivity and compromise core systems and information. Stay safe at home with these 6 Cyber Security Tips for Remote Workers. […]
Computer Tip of the Day: Internet Speed And Your Business

If a positive internet “surfing” experience is desired, whether at home or at the place of employment, the following points should be considered: Bandwidth Latency Computer health Internet Browser Extensions Bandwidth is the allowance of data that may be downloaded per given unit of time. For example, if a typical DSL plan of 1-20 Megabits/sec is purchased, […]

